Introduction
In the current era of rapid digital transformation, the protection of cloud-native infrastructure is considered a top priority. As more services are migrated to containerized environments, the potential for security breaches is increased. Kubernetes is recognized as the leading platform for managing these containers, but its complexity often leads to vulnerabilities. To address these risks, specialized expertise is required.
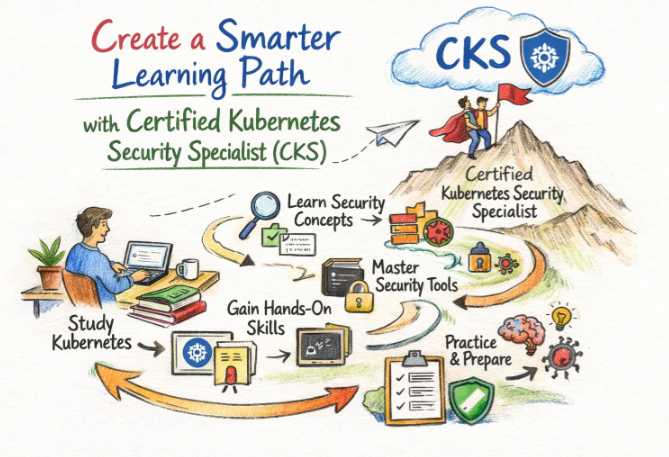
The Certified Kubernetes Security Specialist (CKS) program is designed to meet this specific demand. It is not merely a test of knowledge but a demonstration of the ability to defend a cluster against real-world threats. This guide is provided to offer a comprehensive look at the path toward achieving this elite status.
Defining the Certified Kubernetes Security Specialist (CKS)
The Certified Kubernetes Security Specialist (CKS) is a performance-based certification that validates a professional’s competency in securing container-based applications. It is overseen by the Cloud Native Computing Foundation (CNCF) in collaboration with The Linux Foundation.
The certification process involves a hands-on exam where security configurations must be applied in a simulated production environment. It is widely regarded as the gold standard for security professionals working within the Kubernetes ecosystem.
Relevance in the Modern Cloud and Automation Landscape
The reliance on automated pipelines and cloud infrastructure has made security an indispensable component of the software lifecycle.
- Risk Reduction: Through the application of CKS principles, the likelihood of a catastrophic data leak is minimized.
- Regulatory Compliance: Technical controls are established to ensure that strict data protection laws are followed.
- Operational Integrity: Systems are hardened to ensure that services remain available even when under attack.
The Strategic Value of Certifications for Leadership and Engineers
Professional certifications are viewed as a benchmark for excellence. For the individual engineer, it serves as a verified record of technical mastery. For the engineering manager, it provides a structured way to ensure the team is equipped to handle modern security challenges.
- Career Advancement: Access to high-level security roles is often granted to those who hold verified credentials.
- Standardized Knowledge: A common baseline of security best practices is established across the entire organization.
- Market Competitiveness: The ability to secure complex environments is highly sought after in the global job market.
Selecting DevOpsSchool for Professional Advancement
The decision to choose a training partner is often based on the quality of hands-on experience provided. DevOpsSchool is selected by thousands of professionals because a deep, practical understanding of security is prioritized over simple rote learning.
Expert mentorship is provided by industry veterans who understand the nuances of production-grade Kubernetes. The learning environment is designed to simulate the actual exam, ensuring that candidates are fully prepared for the pressure of a performance-based test. Furthermore, continuous support is offered to help students translate their certification into real-world career success.
Detailed Exploration: Certified Kubernetes Security Specialist (CKS)
What is this certification?
This is a high-level technical credential that confirms the ability to secure a Kubernetes cluster. It focuses on the entire lifecycle, from the initial build and deployment to continuous runtime monitoring.
Who should take this certification?
This path is recommended for those who have already achieved the Certified Kubernetes Administrator (CKA) status. It is designed for Cloud Security Engineers, DevOps leads, and SREs who are responsible for maintaining secure production environments.
Comprehensive Certification Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| DevOps | Intermediate | Automation Engineers | Basic Linux | Orchestration & CI/CD | 1st |
| SRE | Advanced | Reliability Leads | CKA Core | Observability & Hardening | 2nd |
| DevSecOps | Specialist | Security Architects | CKA & Linux | Threat Modeling & Defense | 3rd |
| AIOps/MLOps | Niche | AI/ML Engineers | Data Science | Model Protection | Parallel |
| DataOps | Specialist | Data Architects | SQL / Cloud | Pipeline Encryption | Post-CKA |
| FinOps | Strategic | Finance Managers | Cloud Basics | Resource Optimization | Any Time |
Skills Acquired through this Journey
- The Kubernetes API server is hardened against unauthorized access.
- Supply chain security is managed through advanced image signing and scanning.
- The host system is secured using kernel-level profiles like AppArmor and Seccomp.
- Ingress and Egress traffic are strictly controlled via Network Policies.
- Sensitive data is protected through the secure management of secrets and encryption.
- System audits are performed to detect and mitigate misconfigurations.
Real-World Projects Post-Certification
- A “Zero Trust” architecture is implemented within a multi-cluster environment.
- Automated security scanning is integrated into an enterprise Jenkins pipeline.
- A real-time threat detection system is deployed using Falco to monitor suspicious activity.
- A Governance, Risk, and Compliance (GRC) framework is applied to a production Kubernetes cluster.
- Admission controllers are configured to prevent the deployment of non-compliant containers.
Strategic Preparation Plans
7–14 Days Intensive Plan
- The CKS curriculum is reviewed for core knowledge gaps.
- Two hours are spent daily on perfecting the configuration of Network Policies.
- Documentation search techniques are practiced to save time during the exam.
- A full simulation of the exam environment is completed once.
30 Days Balanced Plan
- One domain of the exam is mastered every week.
- Weekly lab sessions are conducted to implement runtime security tools.
- The official Kubernetes security documentation is studied thoroughly.
- Mock exams are used to identify and fix areas of weakness.
60 Days Comprehensive Plan
- Deep-dive sessions are held into advanced topics like OPA Gatekeeper.
- A personal security lab is built from scratch to test various attack scenarios.
- Community forums and whitepapers are reviewed to understand recent vulnerabilities.
- Multiple iterations of the exam simulator are performed until a high score is consistently achieved.
Common Preparation Pitfalls
- Prerequisite Oversight: The CKS cannot be scheduled if a valid CKA certification is not maintained.
- Documentation Reliance: Too much time is wasted searching through the docs during the exam instead of relying on practiced knowledge.
- Context Management: Tasks are accidentally performed in the wrong cluster context, leading to lost marks.
- Tooling Unfamiliarity: Candidates are often unprepared for tools like
vimorjournalctlin a restricted environment.
Recommended Next Steps
- Same Track: The CKAD (Certified Kubernetes Application Developer) is pursued to understand developer-level security.
- Cross-Track: Terraform Associate is taken to master Infrastructure as Code (IaC) security.
- Leadership Track: The CISM (Certified Information Security Manager) is pursued for a transition into executive security leadership.
Customizing Your Professional Path
DevOps Path
This path is tailored for those who manage the delivery of software. The CKS ensures that the speed of delivery is matched by a high standard of security, preventing the deployment of vulnerable code.
DevSecOps Path
The focus here is entirely on the integration of security into every phase of development. This is the natural progression for engineers who wish to specialize in cybersecurity within cloud-native environments.
Site Reliability Engineering (SRE) Path
For the SRE, security is viewed as a prerequisite for reliability. This path is chosen by those who manage high-availability systems where a security breach is considered a failure in reliability.
AIOps / MLOps Path
As AI models are increasingly deployed on Kubernetes, their protection becomes critical. This path is followed by ML engineers who need to secure their proprietary models and training data.
DataOps Path
The protection of data integrity during movement is the core focus here. This path is best for data engineers who work with highly sensitive information in financial or medical sectors.
FinOps Path
Financial governance is linked to security; unmonitored resources are often a sign of a breach. This path is for those who manage the financial health of the cloud and need to understand security-related costs.
Role-Based Certification Mapping
| Role | Primary Goal | Recommended Cert | Strategic Next Step |
| DevOps Engineer | Automation | CKA | CKS |
| Site Reliability Engineer | Availability | CKS | Cloud Architect |
| Platform Engineer | Infrastructure | CKS | HashiCorp Terraform |
| Cloud Engineer | Versatility | AWS SysOps | CKS |
| Security Engineer | Defense | CKS | CISSP |
| Data Engineer | Integrity | Data Engineering | CKS |
| FinOps Practitioner | Cost Control | FinOps Cert | CKS |
| Engineering Manager | Leadership | CKS | PMP |
Next Certifications for Continuous Growth
For every learner, a multi-track approach is recommended to ensure a well-rounded profile:
- Same-Track Certification: The CKAD is recommended to ensure that security is understood from the perspective of the application developer.
- Cross-Track Certification: A Certified Cloud Security Professional (CCSP) is suggested to broaden security knowledge beyond just Kubernetes.
- Leadership-Focused: The Certified Information Systems Auditor (CISA) is recommended for those moving into governance and auditing roles.
Leading Training and Certification Institutions
DevOpsSchool
High-quality, hands-on training for the CKS is delivered by this institution. The curriculum is built around real-world scenarios to ensure students are ready for the industry. Mentorship is provided by experts who have significant experience in global tech environments.
Cotocus
Specialized training and consulting services are provided with a focus on cloud-native technologies. Their workshops are designed to help professionals bridge the gap between theory and practice. Cotocus is known for its rigorous approach to technical excellence.
ScmGalaxy
A comprehensive platform for SCM and DevOps professionals is maintained by ScmGalaxy. A wealth of free learning resources and community support is offered to help engineers stay updated. It is a vital hub for those pursuing professional certifications.
BestDevOps
Bootcamps and focused training modules are developed to accelerate the learning curve for engineers. Individualized attention is provided to ensure that every student reaches their full potential. The programs are highly regarded for their practical relevance.
devsecopsschool.com
A specialized educational platform dedicated entirely to DevSecOps is found here. The most advanced security tools and methodologies are taught to prepare engineers for modern threats. It is an essential resource for CKS candidates.
sreschool.com
The principles of reliability and automation are taught at this institution. Courses are structured to help engineers build systems that are both resilient and secure. It is the preferred choice for aspiring Site Reliability Engineers.
aiopsschool.com
Training on the application of AI in operational environments is provided. The focus is placed on using intelligent systems to manage and secure large-scale infrastructures. It represents the future of automated operations.
dataopsschool.com
The management of data pipelines is the primary focus of this school. Students are trained to build secure and efficient systems for data movement and storage. It is ideal for data professionals in compliance-heavy industries.
finopsschool.com
Financial management in the cloud is taught through a technical lens. Professionals are trained to optimize spending while maintaining the highest security standards. It is a critical institution for modern cloud business leaders.
Frequently Asked Questions (FAQs)
- Is the CKS exam harder than the CKA?
The CKS is generally considered more difficult because it requires a deeper understanding of security tools outside of basic Kubernetes. - What is the minimum requirement to take the CKS?
An active CKA certification must be possessed by the candidate before they can attempt the CKS. - How long does a candidate have to complete the exam?
A total of two hours is provided to complete the performance-based tasks. - Are specific security tools tested in the exam?
Yes, tools such as Falco, Trivy, and Kube-bench are commonly included in the curriculum. - Is the CKS valuable for job seekers in the USA and Europe?
Absolutely, global organizations are actively seeking certified specialists to secure their cloud-native stacks. - Can the exam be taken in multiple languages?
The exam is primarily offered in English, though some local language support may be available depending on the region. - What is the passing score for the CKS?
A score of at least 67% is required to be considered successful in the examination. - Is a free retake included in the exam fee?
Usually, one free retake is provided if the first attempt is not successful. - How often is the CKS curriculum updated?
The curriculum is updated periodically by the CNCF to reflect the latest versions of Kubernetes. - Does the CKS expire?
The certification is valid for a period of two years, after which recertification is required. - Are cloud provider services like EKS or GKE tested?
No, the exam is platform-agnostic and focuses on the upstream version of Kubernetes. - Is it possible to prepare for CKS while working full-time?
Yes, with a structured plan and consistent daily practice, many professionals achieve certification while employed.
FAQs for Certified Kubernetes Security Specialist (CKS)
- What is the primary focus of the CKS exam?
The primary focus is placed on the ability to harden a cluster, secure the supply chain, and monitor runtime threats. - How is image scanning assessed in the CKS?
Candidates are often required to use tools like Trivy to identify vulnerabilities in container images and prevent their deployment. - Is the use of Admission Controllers tested?
Yes, the configuration of ImagePolicyWebhook and other admission controllers is a key part of the security curriculum. - What role does RBAC play in the CKS?
Role-Based Access Control is used to enforce the principle of least privilege, ensuring that users and services have only the necessary permissions. - Are Network Policies essential for the CKS?
Yes, a deep understanding of how to isolate pod communication using Network Policies is required. - How is secret management handled in the CKS?
The secure storage and encryption of secrets at rest within the etcd database are common topics. - Is runtime security monitoring a significant part of the test?
A significant portion of the exam is dedicated to detecting suspicious activity using system-level monitoring tools. - Can the official Kubernetes documentation be accessed during the exam?
Access to the official Kubernetes documentation and specific allowed security tool sites is permitted during the exam.
Testimonials
Aarav A completely new perspective on cluster security was gained. The skills acquired have already been used to harden our company’s production environment. The training was instrumental in passing the exam on the first attempt.
Meera The transition from a developer to a security specialist was made possible through this certification. The depth of the curriculum ensured that all aspects of the container lifecycle were covered. Career clarity was significantly improved.
Julian The hands-on nature of the CKS training provided the confidence needed to handle complex security incidents. Practical knowledge of tools like Falco was the most valuable takeaway. It is highly recommended for all SREs.
Sanjay My technical profile was greatly enhanced by the addition of the CKS credential. The ability to demonstrate security expertise has opened doors to senior roles in the global market. The investment in learning has already paid off.
Elena Strategic security planning for our cloud infrastructure is now a standard practice. The certification provided a structured framework for identifying and mitigating risks. Professional credibility within the engineering team was boosted.
Conclusion
The pursuit of the Certified Kubernetes Security Specialist (CKS) certification is a strategic move for any engineer in the cloud-native space. It represents a mastery of the tools and techniques required to protect the modern digital infrastructure. By securing this credential, a professional is not just passing a test; they are becoming a vital guardian of organizational data.
Long-term career benefits are unlocked through this specialized knowledge. Continuous learning and strategic planning are highly encouraged for those who wish to remain at the forefront of the industry. The journey toward becoming a security specialist is a rewarding path that offers both personal and professional growth.